Enterprise-grade Data Security and Compliance
Enterprise users worldwide trust FlytBase to safeguard their drone docks and data.
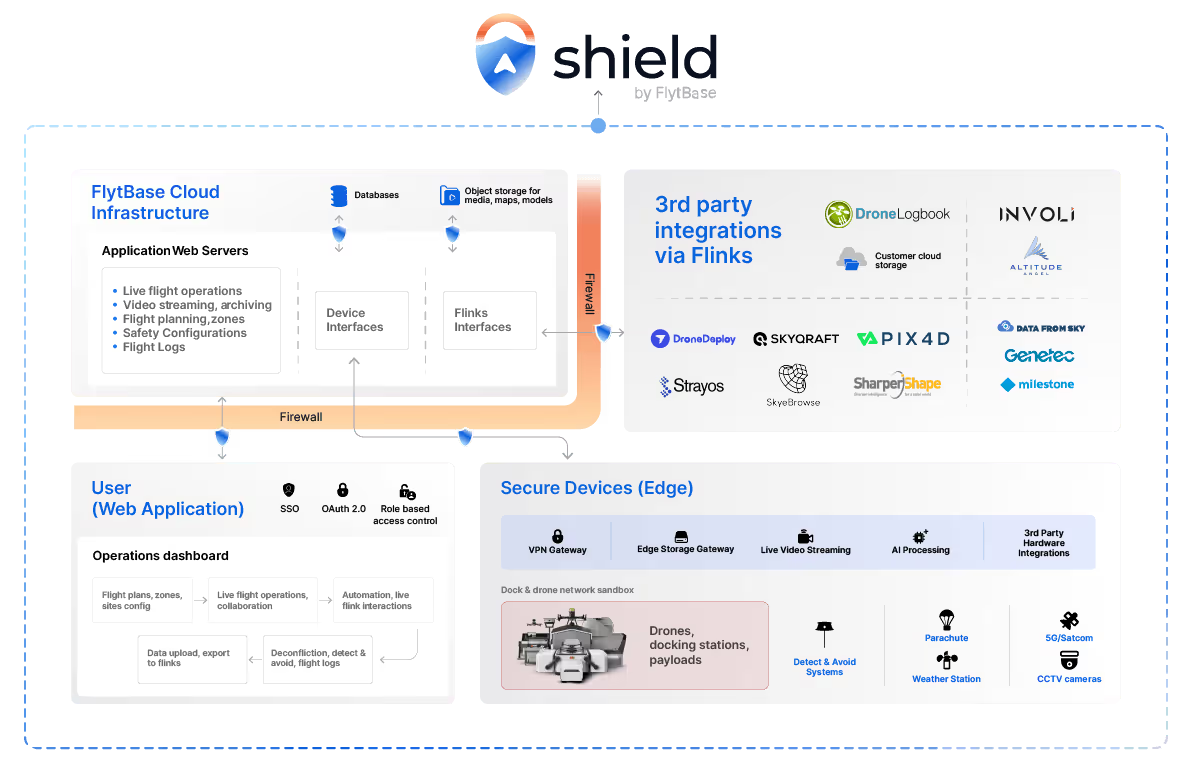
FlytBase Shield provides multi-layer protection at the edge, on the cloud, on-premises, or via an air-gapped system. FlytBase cyber security experts make your IT compliance and cyber security assessments swift and easy.
Download FlytBase Shield White paperFlytBase Shield provides multi-layer protection at the edge, on the cloud, on-premises, or via an air-gapped system. FlytBase cyber security experts make your IT compliance and cyber security assessments swift and easy.
How FlytBase Shield keeps your data secure
With multiple layers of protection that includes secure data transfer, encryption, network configuration, and application-level controls, FlytBase platform is designed with security in mind. We also use tools to help us enforce compliance with our internal security policies.
Compliances and Certifications
FlytBase complies with essential industry standards, privacy laws, and certifications.
Pillars of FlytBase Shield
Data protection
Data isolation
Each user's data in FlytBase is securely separated and accessible only to authorized users.
Data encryption
FlytBase encrypts data at rest and in transit using AES-256 and TLS 1.2 protocols, respectively.
Recovery and Redundancy
Operational data is stored across multiple secure locations with continuous replication and backups
Network security
Firewalls on all communication channels to prevent unauthorized access, restrict malicious attackers, and block communication with any unauthorised servers.
Application security
Vulnerability Assessment
Regular third-party vulnerability assessments are performed to identify and resolve security threats and weaknesses.
Penetration Testing
FlytBase undergoes application and its underlying infra penetration tests by independent security specialists.
Development Standards
FlytBase adheres to the coding standards set by the OWASP and incorporates Static Application Security Testing (SAST).
IT compliance and support
CIS, NIST frameworks followed to ensure compliance with industry-agreed cybersecurity standards. FlytBase experts provide on-demand support to meet IT compliance requirements for enterprises.
Identity and User Management
Roles and Permissions
Role-based access control (RBAC) are offered for different kinds of dashboard users (admin, operator, viewer).
OAuth Login
Authenticate seamlessly using your existing Google or Microsoft enterprise credentials. Streamline access with trusted OAuth 2.0 integration while maintaining security and user convenience.
Enterprise Single sign-on (SSO)
Authenticate through your enterprise identity management system for centralized authentication and access control. Maintain security compliance, enforce organizational policies, and enable seamless integration with your existing IT infrastructure.
Need additional security?
FlytBase offers flexible deployment options, including the option to operate on a separately managed AWS environment with physical isolation from the shared infrastructure of our multi-tenant cloud offering, giving an additional layer of security and privacy.
Flexible Deployment Options

Cloud
FlytBase Cloud provides cost-effective access with enterprise-level security. It complies with SOC2 Type II, ISO 27001, and GDPR standards, and enables integration with private cloud storage.

In-country Cloud
Deploy FlytBase in your own country’s cloud to ensure compliance with data residency norms, data security, & the ability for customers to integrate with their preferred applications.

On-premises
Self-host FlytBase on a private server for highly secure & confidential projects. Meet cyber security compliance requirements and have complete control over your drone data.

Air-Gapped
FlytBase Air-Gapped operates offline, isolated from external networks, ensuring data security. Ideal for sensitive applications that require maximum protection.





-min.webp)

