Get Your Free Drone Autonomy Guide Today!

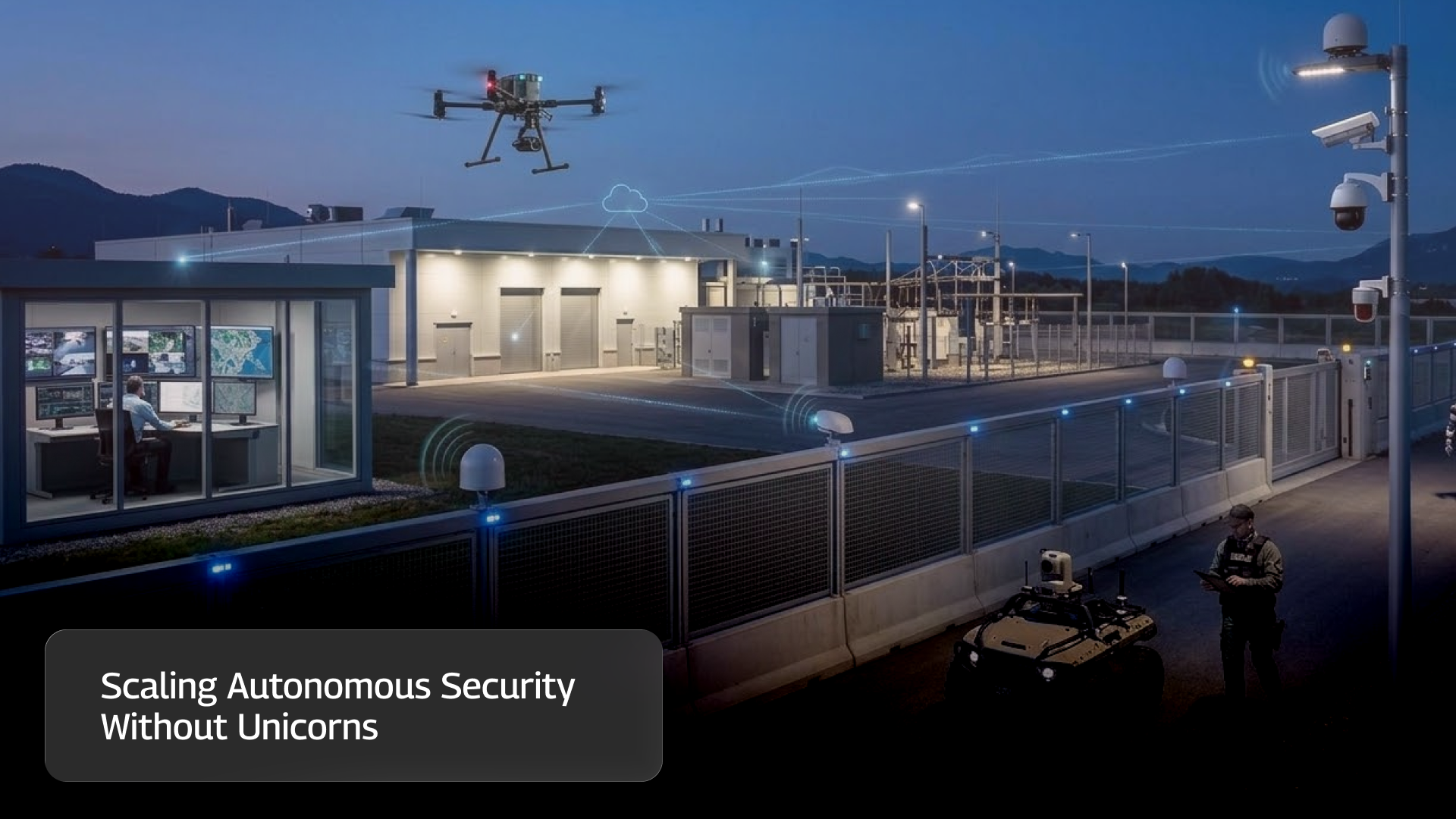
The first autonomous drone deployment at a security site usually works. The drone launches. Patrols run overnight. The dock operates reliably. The pilot project delivers exactly what it promised. Then the organization tries to expand to ten or twenty sites. That is where things begin to stall.
The obstacle is rarely the drone itself. It is the expertise required to operate the system.
Many early deployments succeed because of a very specific kind of employee. Someone who understands both security operations and drone operations. They know how patrol coverage should work, how incidents are handled, and what the facility needs to monitor. At the same time, they understand flight safety, mission planning, hardware configuration, and regulatory requirements. Inside many organizations, this person has an informal name.
The unicorn. Unicorns make the first deployment possible. But building a program around them creates a structural problem. They are rare, difficult to replicate, and impossible to scale.
Two Different Worlds
Security operations and drone operations are two completely different domains. Security professionals think in terms of threat assessment, patrol logic, coverage gaps, and incident response. Their job is to understand what needs to be monitored and how to react when something goes wrong.
Drone operators live in another world. They focus on mission planning, airspace compliance, flight safety, payload configuration, and aviation regulations. The overlap between these two knowledge areas is small. When someone understands both, they can translate between the two systems. They know how to turn a security request into a drone mission and how to interpret drone operations for a security team. But that overlap is fragile. Most organizations have only one or two people who truly sit in that intersection.
When scaling begins, the limits quickly become clear.
The Expertise Trap
To move beyond the unicorn model, organizations often try one of two approaches. The first option is to train drone pilots to understand security operations. On the surface, this seems logical. If the pilot understands the facility and the security requirements, they should be able to design patrol missions that meet those needs.
In practice, the pilot often gains only a surface-level understanding of security. They can capture footage, but they may not fully understand threat patterns, patrol priorities, or what the security team is actually looking for.
As requests grow more complex, the pilot becomes the bottleneck.
The second option is to train security teams to operate drones. This creates a different problem. Drone operations are not static. Regulations evolve. Airspace restrictions change. Hardware platforms and sensors continue to develop. Mission planning and safety procedures introduce an entirely new operational discipline.
Security professionals are suddenly expected to become aviation operators while still doing their primary job. In many organizations, the cognitive load becomes unrealistic. What started as a security program begins to resemble a small aviation department. Neither path solves the scaling challenge.
One creates pilots who do not fully understand security. The other asks security professionals to become drone specialists. Both approaches depend on individuals learning two different professions.
A Different Model
There is another option. Instead of forcing individuals to span both domains, organizations can separate the expertise entirely. Security operators remain focused on security. Drone operators remain focused on flight operations. A system interface sits between them, translating requests from one world into actions in the other.
In this model, the security team works entirely in the language they already understand. They define patrol zones, coverage schedules, incident responses, and inspection requests. Those requests become structured operational jobs for the drone operations team. The pilots do not need to understand the full security context. Their role is to execute missions safely, manage the fleet, and ensure regulatory compliance.
The two groups interact through the system rather than through shared expertise.
From Requests to Results
Once this separation exists, the workflow becomes far simpler. Security operators submit requests in security terms. A patrol, an incident verification, or a fence inspection is defined by location, priority, and what needs to be observed. The drone operations team receives that request as an operational task. They handle flight planning, safety checks, and execution. When the mission is complete, the results return to the security team in their own operational context. Live video, automated alerts, and patrol coverage reports appear inside the same workflows already used in a security operations center. From the operator’s perspective, the drone becomes just another sensor in the security system.

The Scaling Breakthrough
This separation changes the scaling equation completely. In the unicorn model, ten sites depend on one or two highly specialized individuals. If those people become overloaded or leave the organization, the program slows or stops. In the separation model, each facility’s security team interacts with the system through familiar workflows. A small centralized drone operations team can manage missions across many sites. Adding a new location does not require finding another unicorn.
It simply requires connecting another security operation to the same infrastructure. Security professionals continue doing security work. Drone operators focus on aviation operations. The system handles the translation between the two. When organizations reach this point, autonomous security programs finally begin to scale. Because the program is no longer built around unicorns. It is built around separation.
FAQs
Find quick answers to common questions about compatibility, setup, features, and pricing



.webp)
.svg)
.webp)


.png)
